The WTF Series: Encryption and Apple’s predicament
March 21, 2016 | Ben Kittrell

For those of you who have been living under a rock the last month, there’s a “little” snafu going on between Apple and the FBI. The FBI handed Apple a court order demanding access to the password-protected iPhone of a mass shooter.
In an open letter to customers, Apple CEO Tim Cook explained that the company had and would continue to deny the order. It would require Apple to build a backdoor into the iPhone’s encryption, compromising the security of all iPhones, he said.
“The implications of the government’s demands are chilling,” Cook wrote. “If the government can use the All Writs Act to make it easier to unlock your iPhone, it would have the power to reach into anyone’s device to capture their data.”
So, what is encryption anyway?
All of your data is stored on a hard drive somewhere. Without encryption, a hacker could bypass your passcode to see anything stored on your phone, such as photos, location history, credit card information and emails.
Encryption basically jumbles up your data so that it’s unreadable to anyone with direct access to it. Even if someone physically pulled out your phone’s hard drive, the data would be useless without a special key that only you own — in the iPhone’s case, your password. This key is used to jumble up the data, so it’s the only way to make it readable again.
In iOS 8, the software that runs the iPhone, Apple decided to encrypt your data automatically. Without your passcode, even Apple can’t access your data.
Is encryption safe?
For more from a security expert, I spoke with my friend Chris Cooley, director of business development for SpiderOak. The Kansas City-based tech firm uses encryption to provide secure backup and communication tools. I asked Cooley his opinion on whether encryption really works. His response? Sometimes.
“It’s important to know that the strength of encryption depends a great deal on how it is applied,” Cooley said. “It’s not a simple yes or no check box.”
Encryption technology is as secure as it gets. But most hackers don’t look for flaws in tech; they look for flaws in humans.
“We’ve all seen the images of little Johnny using his secret decoder ring to turn random letters into a secret message,” Cooley continued. “In the digital age, much of the encryption happens server-side, meaning that that decoder ring (the key) is on the server. As you can imagine, a coded message in the same box as the decoder ring is less than ideal.”
“Some companies use a single set of keys, just one decoder ring, for all encryption,” he added. “If it gets copied or stolen, everyone now has a problem. Other organizations will create a new decoder ring for each user.”
Encryption is safe, as long as your keys are managed properly. As Cooley says, “A military-grade front door is near worthless if you’re just leaving the key under the front mat.”
Where else is encryption used?
We all know that you shouldn’t enter private information on a website unless you see the secure “lock” icon in the address bar, right? Right?! That lock means that all of the information that travels from your computer to the website is encrypted, and no one can read it along the way.
This technology is called Secure Socket Layers or SSL and is becoming a standard for all websites, even if you’re not collecting credit card data. Without it, anyone at the coffee shop could hijack your Facebook login and take those quizzes for you.
Encryption is increasingly incorporated into almost every electronic device that stores valuable personal information. Apple isn’t just fighting for the security of one iPhone, or even for the security of all its iPhones. It’s fighting to prevent a legal precedent of government requiring a backdoor to every device you own. And if you think that’s scary for the government to have control of, imagine if those “keys” eventually fell into the wrong hands.
Ben Kittrell is the co-founder of Doodlekit and an advisor for startups and small businesses. Kittrell also is host of Spare Room Radio, a podcast that features Kansas City entrepreneurs.
Featured Business

2016 Startups to Watch
stats here
Related Posts on Startland News
EDCKC boasts right team at the right time, CEO says as agency rebuilds its reputation
With 18 months of foundational work now laid, Tracey Lewis said, the Economic Development Corporation of Kansas City is well on its way to rebuilding the trust, respect, and effective communication needed to execute the agency’s economic development goals. That takes repairing bridges between the City of KCMO and the EDCKC, he said, as well…
PayIt forward: Kansas renews contract with KC tech company that took DMV headaches off the road
For the more than 1 million Kansans who’ve already avoided long lines at the DMV thanks to PayIt’s award-winning digital payments platform, that experience — and others — will only get more convenient with the mobile-first technology’s Sunflower State renewal through at least 2026. PayIt this week announced a new deal with the State of…
Bill to help ease veterans’ transition from military to business passes US House with KC leaders in the trenches
A legislative effort to boost support for U.S. military veterans pursuing a new chapter as entrepreneurs now heads to the U.S. Senate — buoyed by broad partisan support and championed by two members of Kansas City’s congressional delegation. The Successful Entrepreneurship for Reservists and Veterans SERV Act successfully passed in the U.S. House of Representatives this…
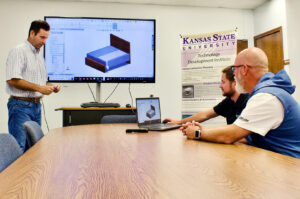
Sleep tech designed to combat night sweats moves toward consumer market with KS bedfellows
A Leawood company’s bed-based sleep technology — designed to reduce night sweats and help people better regulate their temperatures while they sleep — is headed to market in early 2024 with backing from the Kansas angel tax credits program and a swelling pre-seed round, said Win Hansen. Rairflow, Inc., which designed and developed prototypes for…